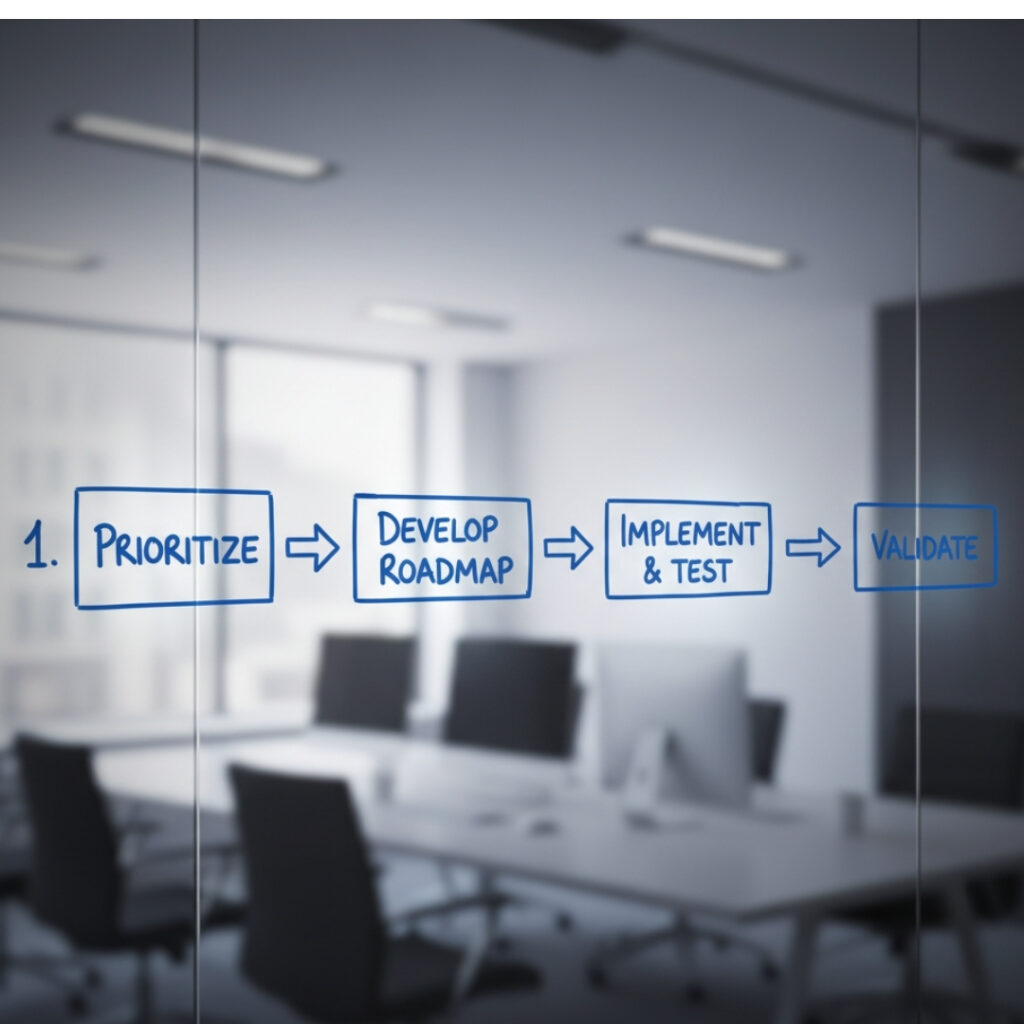
When a vulnerability assessment is complete, the report in your hands is only the beginning. True security lies in the strategic steps you take next to close those gaps. Moving “beyond the scan” and into action is where Cyberstone’s expertise comes into play for your team. This 4-step framework helps you prioritize and fix weaknesses decisively.
Prioritize Findings by Risk Score and Business Impact
A lengthy list of vulnerabilities can feel overwhelming, but they are not all created equal. You must first prioritize them using standardized risk scores (like CVSS) combined with your unique business context. Work with Cyberstone’s IT consulting experts to focus remediation efforts on high-risk items that directly threaten critical systems or sensitive data.
Develop a Clear, Phased Remediation Roadmap
Rushing into fixes without a plan can introduce new risks or cause system downtime. Instead, create a structured, phased roadmap that addresses vulnerabilities systematically. This involves defining specific owners, setting realistic deadlines, and ensuring that all necessary resources are allocated. Cyberstone helps you integrate remediation into your existing IT operations seamlessly.
Implement and Test Patches and Configuration Changes
Remediation often involves deploying patches, updating software, or hardening system configurations. It is crucial to test these changes in a non-production environment first to confirm they solve the issue without breaking functionality. This validation step is non-negotiable for maintaining system stability while improving your security posture against future threats.
Conduct Post-Remediation Validation and Re-Assessment
Once changes are implemented, the final and most critical step is validation. Simply applying a patch isn’t enough; you must verify the vulnerability is actually closed. Cyberstone performs a targeted re-assessment or mini-vulnerability assessment to ensure the fix was successful and to confirm no new weaknesses were inadvertently created during the process.
The remediation phase is the critical link between knowing a risk exists and actually securing your enterprise. By following this structured four-step process, your organization moves from passive report reading to proactive security management. Partner with Cyberstone for expert guidance and IT consulting to transform your vulnerability data into an unshakeable defense strategy.